Geographic Calculator Software
Geographic Calculator
Geodetic Calculation & Transformation



Services

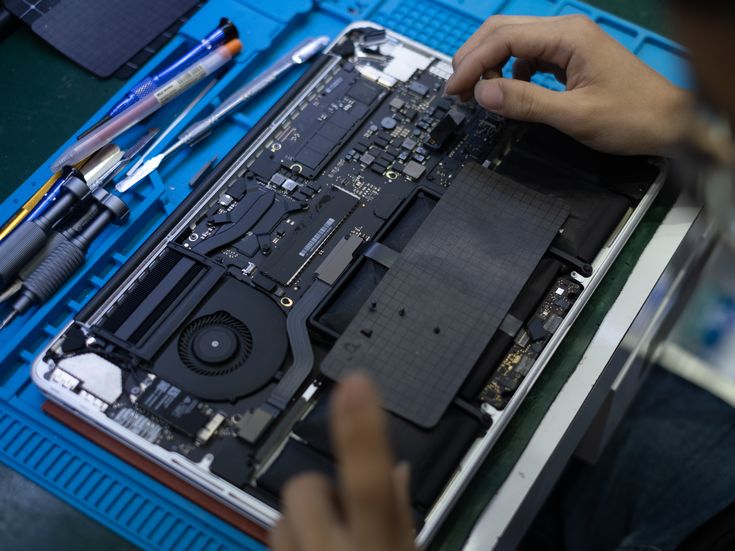
Service ur Laptop or Notebook, PC, UPS, Printer, Scanner, and Other IT Product Here
All Products
Ansys Fluent
Fortanix Security SoftwareConfidential AI Confidential AI is a new platform to securely develop and deploy AI models on sensitive data using confidential computing. The solution provides data teams with infrastructure, software, and workflow orchestration to create a...
GeoStudio Flow
virtuosity bentley SoftwareGeoStudio Flow Seequent | The Bentley Subsurface Company Seequent is the subsurface software company within Bentley Systems. Together, we’re helping build a more resilient future by connecting the built world above ground with the hidden...
GeoStudio 3D
virtuosity bentley SoftwareGeoStudio 3D Seequent | The Bentley Subsurface Company Seequent is the subsurface software company within Bentley Systems. Together, we’re helping build a more resilient future by connecting the built world above ground with the hidden world...
Confidential AI
Fortanix Security SoftwareConfidential AI Confidential AI is a new platform to securely develop and deploy AI models on sensitive data using confidential computing. The solution provides data teams with infrastructure, software, and workflow orchestration to create a...
Confidential Data Search
Fortanix Security SoftwareConfidential Data Search An industry-first solution for searching regulated data in encrypted databases at scale When it comes to analyzing sensitive data such as financial or medical datasets, organizations have to compromise on security or...
GeoStudio 2D
virtuosity bentley SoftwareGeoStudio 2DSeequent | The Bentley Subsurface Company Seequent is the subsurface software company within Bentley Systems. Together, we’re helping build a more resilient future by connecting the built world above ground with the hidden world...
Filesystem Encryption
Fortanix Security SoftwareFilesystem Encryption Keep individual files and folders safe to defend against malicious actors and meet compliance. To enhance data loss prevention and comply with privacy regulations, businesses are constantly looking to strengthen their...
Transparent Database Encryption
Fortanix Security SoftwareTransparent Database Encryption Fortanix simplified database encryption by providing a single integrated key management and hardware security module (HSM) to manage and store cryptographic keys across all your databases. In times of...
Tokenization Fortanix
Fortanix Security SoftwareTokenization Fortanix Tokenization / Format-Preserving Encryption Protect sensitive data and adhere to regulations with a secure and scalable data tokenization solution. In times of relentless cyberattacks and rampant online fraud, data...
Secrets Management
Fortanix Security SoftwareSecrets Management An enterprise-ready secret management solution that lets your DevOps and security teams securely store, control and manage secrets, credentials, certificates, API keys, and tokens outside the source code in a FIPS 140-2...
EasyPower
virtuosity bentley SoftwareEasyPowerAutomated Power System SoftwareTime-saving features and incredibly intuitive tools reduce days of work into mere minutes. Model three-phase, single-phase, and DC equipment on an integrated one-line diagram. Instantly finish even the...
Code Signing
Fortanix Security SoftwareCode Signing Secure Your Code-Signing Process Fortanix enables developers to cryptographically sign code to verify the authenticity and integrity of applications, ensuring they are not altered or corrupted. Code signing using digital...